Disclaimer: Don't hack anything where you don't have the authorization to do so. Stay legal.
Ever since I bought my first Android device, I wanted to use the device for WEP cracking. Not because I need it, but I want it :) After some googling, I read that you can't use your WiFi chipset for packet injection, and I forgot the whole topic.
After a while, I read about hacking on tablets (this was around a year ago), and my first opinion was:
Ever since I bought my first Android device, I wanted to use the device for WEP cracking. Not because I need it, but I want it :) After some googling, I read that you can't use your WiFi chipset for packet injection, and I forgot the whole topic.
After a while, I read about hacking on tablets (this was around a year ago), and my first opinion was:
"This is stupid, lame, and the usage of that can be very limited".
After playing one day with it, my opinion just changed:
"This is stupid, lame, the usage is limited, but when it works, it is really funny :-)"
At the beginning I looked at the Pwn Pad as a device that can replace a pentest workstation, working at the attacker side. Boy was I wrong. Pwn Pad should be used as a pentest device deployed at the victim's side!
At the beginning I looked at the Pwn Pad as a device that can replace a pentest workstation, working at the attacker side. Boy was I wrong. Pwn Pad should be used as a pentest device deployed at the victim's side!
You have the following options:
- You have 1095 USD + VAT + shipping to buy this Pwn Pad
- You have around 200 USD to buy an old Nexus 7 tablet, a USB OTG cable, a USB WiFi dongle (e.g. TP-Link Wireless TL-WN722N USB adapter works).
In my example, I bought a used, old 2012 Nexus WiFi. Originally I bought this to play with different custom Android ROMs, and play with rooted applications. After a while, I found this Pwn Pad hype again and gave it a shot.
The Pwn Pad community edition has an easy-to-use installer, with a proper installation description. Don't forget to backup everything from your tablet before installing Pwn Pad on it!
I don't want to repeat the install guide, it is as easy as ABC. I booted a Ubuntu Live CD, installed adb and fastboot, and it was ready-to-roll. I have not measured the time, but the whole process was around 20 minutes.
The internal WiFi chipset can be used to sniff traffic or even ARP poisoning for active MiTM. But in my case, I was not able to use the internal chipset for packet injection, which means you can't use it for WEP cracking, WPA disauth, etc. This is where the external USB WiFi comes handy. And this is why we need the Pwn Pad Android ROM, and can't use an average ROM.
There are two things where Pwn Pad really rocks. The first one is the integrated drivers for the external WiFi with monitor mode and packet injection capabilities. The second cool thing is the chroot wrapper around the Linux hacking tools. Every hacking tool has a start icon, so it feels like it is a native Android application, although it is running in a chroot Kali environment.
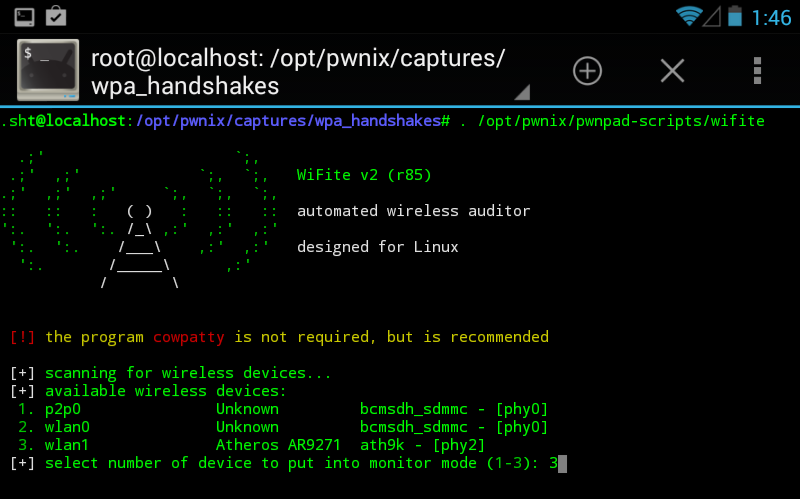
Wifite
The first recommended app is Wifite. Think of it as a wrapper around the aircrack - airmon - airodump suite. My biggest problem with WEP cracking was that I had to remember a bunch of commands, or have the WEP cracking manual with me every time I have to crack it. It was overcomplicated. But thanks to Wifite, that is past.
In order to crack a WEP key, you have to:
- Start the Wifite app
- Choose your adapter (the USB WiFi)
- Choose the target network (wep_lan in the next example)
- Wait for a minute
- PROFIT!
SSH reverse shell
This is one of the key functionalities of the Pwn Pad. You deploy the tablet at the Victim side, and let the tablet connect to your server via (tunneled) SSH.The basic concept of the reverse shells are that an SSH tunnel is established between the Pwn Pad tablet (client) and your external SSH server (either directly or encapsulated in other tunneling protocol), and remote port forward is set up, which means on your SSH server you connect to a localport which is forwarded to the Pwn Pad and handled by the Pwn Pad SSH server.
I believe the best option would be to use the reverse shell over 3G, and let the tablet connect to the victim network through Ethernet or WiFi. But your preference might vary. The steps for reverse shells are again well documented in the documentation, except that by default you also have to start the SSH server on the Pwn Pad. It is not hard, there is an app for that ;-) On your external SSH server you might need to install stunnel and ptunnel if you are not using Kali. The following output shows what you can see on your external SSH server after successful reverse shell.
root@myserver:/home/ubuntu# ssh -p 3333 pwnie@localhost The authenticity of host '[localhost]:3333 ([127.0.0.1]:3333)' can't be established. ECDSA key fingerprint is 14:d4:67:04:90:30:18:a4:7a:f6:82:04:e0:3c:c6:dc. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '[localhost]:3333' (ECDSA) to the list of known hosts. pwnie@localhost's password: _____ ___ _ ___ ___ _____ _____ ___ ___ ___ ___ | _ \ \ / / \| |_ _| __| | __\ \/ / _ \ _ \ __/ __/ __| | _/\ \/\/ /| .` || || _| | _| > <| _/ / _|\__ \__ \ |_| \_/\_/ |_|\_|___|___| |___/_/\_\_| |_|_\___|___/___/ Release Version: 1.5.5 Release Date: 2014-01-30 Copyright 2014 Pwnie Express. All rights reserved. By using this product you agree to the terms of the Rapid Focus Security EULA: http://pwnieexpress.com/pdfs/RFSEULA.pdf This product contains both open source and proprietary software. Proprietary software is distributed under the terms of the EULA. Open source software is distributed under the GNU GPL: http://www.gnu.org/licenses/gpl.html pwnie@localhost:~$
Now you have a shell on a machine that is connected to the victim network. Sweet :) Now Metasploit really makes sense on the tablet, and all other command-line tools.
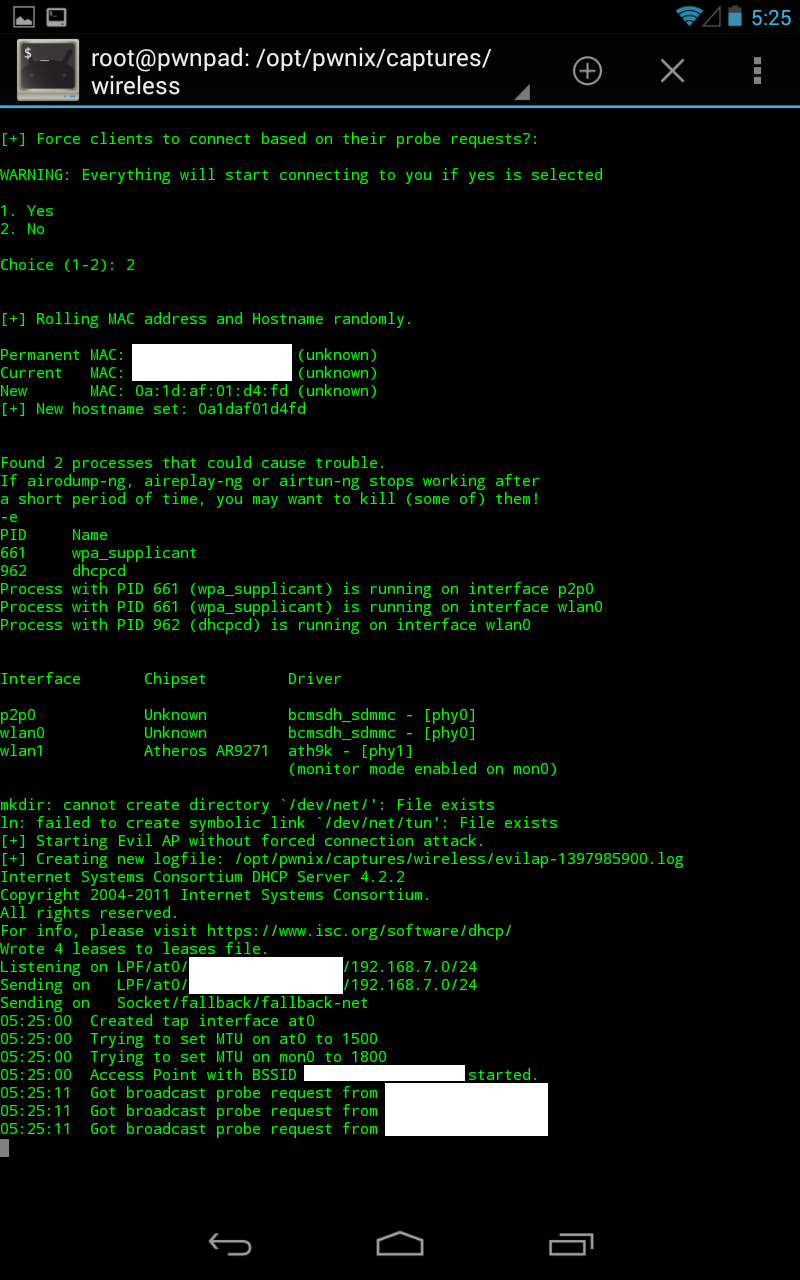
EvilAP and DSniff
Start EvilAP (it is again a wrapper around airobase), choose interface (for me the Internal Nexus Wifi worked), enter an SSID (e.g freewifi), enter channel, choose whether force all clients to connect to you or just those who really want to connect to you, and start.The next step is to start DSniff, choose interface at0, and wait :) In this example, I used a popular Hungarian webmail, which has a checkbox option for "secure" login (with default off). There are sooo many problems with this approach, e.g. you can't check the certificate before connecting, and the login page is delivered over HTTP, so one can disable the secure login checkbox seamlessly in the background, etc. In this case, I left the "secure" option on default off.
In the next tutorial, I'm going to show my next favorite app, DSploit ;)
Lessons learned
Hacking has been never so easy beforeIn a home environment, only use WPA2 PSK
Choose a long, nondictionary passphrase as the password for WPA2
Don't share your WiFi passwords with people you don't trust, or change it when they don't need it anymore
Don't let your client device auto-connect to WiFi stations, even if the SSID looks familiar
I believe during an engagement a Pwn Plug has better "physical cloaking" possibilities, but playing with the Pwn Pad Community Edition really gave me fun moments.
And last but not least I would like to thank to the Pwn Pad developers for releasing the Community Edition!
And last but not least I would like to thank to the Pwn Pad developers for releasing the Community Edition!
Related posts
- Free Pentest Tools For Windows
- Top Pentest Tools
- Hacker Tools For Ios
- World No 1 Hacker Software
- Hacking Tools For Beginners
- Hacking Tools For Windows
- Pentest Tools Url Fuzzer
- Hack Tools 2019
- Hacking Tools Github
- Hacking Tools Windows
- Underground Hacker Sites
- Hacker Security Tools
- Hacking Tools For Windows Free Download
- Pentest Tools Download
- Top Pentest Tools
- Wifi Hacker Tools For Windows
- Pentest Tools Subdomain
- Hacking Tools For Games
- Hacking Tools For Pc
- Hacking Tools For Pc
- Hacking Tools
- Hacking Tools 2020
- Hacking Tools For Kali Linux
- Pentest Tools Website
- Best Hacking Tools 2020
- Github Hacking Tools
- Wifi Hacker Tools For Windows
- Hacker Techniques Tools And Incident Handling
- New Hacker Tools
- Hack Tools
- Best Hacking Tools 2020
- Pentest Tools Review
- What Is Hacking Tools
- Usb Pentest Tools
- Hack Tools Pc
- Hack Tools For Games
- Computer Hacker
- Hacking Tools Online
- Hacking Tools For Beginners
- Hacker Tools
- Hacking Tools Usb
- Pentest Tools Find Subdomains
- Pentest Tools Alternative
- Pentest Tools List
- Github Hacking Tools
- Hacker Tools Software
- Hacking Tools And Software
- Hacker Tools Windows
- Install Pentest Tools Ubuntu
- Underground Hacker Sites
- Pentest Tools Alternative
- Underground Hacker Sites
- Pentest Box Tools Download
- Pentest Tools For Mac
- New Hacker Tools
- Hack Tools Github
- Pentest Tools Apk
- Blackhat Hacker Tools
- Hacking Tools Free Download
- Github Hacking Tools
- Hacker Tools Free
- Hacker Tools Apk
- Hack And Tools
- Pentest Tools Alternative
- Hacking Tools
- Hacking Tools Usb
- Hack Tools Mac
- Hacking App
- Hacker Tools Apk
- Pentest Tools Alternative
- Hacking Tools Online
- Hacker Tools Online
- Game Hacking
- Hacking Tools Download
- Tools For Hacker
- Hacking Tools For Pc
- Hack App
- Hacking Tools Software
- Growth Hacker Tools
- Hacking Tools For Beginners
- Game Hacking
- Hacking Tools Hardware
- Hacker Security Tools
- Kik Hack Tools
- Pentest Tools Apk
- Pentest Tools Kali Linux
- Android Hack Tools Github
- Pentest Box Tools Download
- Pentest Tools Apk
- Pentest Tools Kali Linux
- What Are Hacking Tools
- Hacking Tools Github
- Hackrf Tools
- Hack Tools
- Hacking Tools Free Download
- Pentest Tools Kali Linux
- Hack Tools For Games
- Pentest Tools Open Source
- Hacker Tools For Windows
- Hack Tool Apk
- Hacker Tools 2020
- Hacking Tools For Games
- Tools For Hacker
- Hack Tools For Pc
- Pentest Box Tools Download
- Pentest Tools For Windows
- Hacking Tools And Software
- Pentest Tools For Windows
- Hacker Tools Github
- Android Hack Tools Github
- Hacking App
- Hacking Tools And Software
- Pentest Box Tools Download
- Hacking Tools For Kali Linux
- Hak5 Tools
- Hack App
- Hack Tool Apk
- Hacker
- Hacking Tools For Games
- Free Pentest Tools For Windows
- How To Hack
- Bluetooth Hacking Tools Kali
- Pentest Tools Bluekeep
- Hacking Tools 2020
- Hacking Tools Windows 10
- Hacking Tools
- Pentest Tools Windows
- Android Hack Tools Github
- Pentest Tools Nmap
- Hacking Tools Free Download
- Beginner Hacker Tools
- Hacking Tools Online
- Hackrf Tools
- Pentest Tools Online
- Install Pentest Tools Ubuntu
- Free Pentest Tools For Windows
- Pentest Tools Github
- Hacking Tools Windows
- Pentest Tools Find Subdomains
- Computer Hacker
- Pentest Tools For Mac
- Hacker Tools Mac
- Hacking Tools 2020
- Hacking Tools Mac
- Best Hacking Tools 2019
- Hack Tools For Windows
- Hacker Tool Kit
- Pentest Recon Tools
- Hack Tools Github
- Pentest Tools Android
- Hack Tools For Ubuntu
- Hacker Tools Windows
- Nsa Hack Tools Download
- Game Hacking
- Hacker Tools For Mac
- Tools 4 Hack
- Hacking Tools Software
- Hack Tool Apk
- Hacking Tools Windows
- Hacking Tools Windows 10
- Hacker Tools 2020
- Black Hat Hacker Tools
- Hacking Tools Software
- Hacking Tools For Windows Free Download





No comments:
Post a Comment